I figured it would end up a $159 device but it has landed at $199. My overall opinion remains the same. As a “USG v.Next” it’s alright. As a Protect host, it’s a hot mess.
Category Archives: UniFi Protect
UniFi Disappointment Router?
The UniFi fanbois were aflutter when Ubiquiti released this video promoting an upcoming UniFi Dream Router:
It sounded like a substantial upgrade to the UniFi Dream Machine: WiFi 6, two ports of PoE, 128GB SSD, an SD slot for storage expansion, and the ability to run Protect and other Ubiquiti controllers that haven’t been available to UDM users due to the lack of storage.

Then it hit the Early Access store for $79. Huh?
Continue readingRepeating Old Mistakes
Early last month, my 20-month old UNVR stopped working. I pulled the drives, tried the Reset button, and thanked the Deities that I live in an area where a UNVR is something that I can buy. In a store. On a Sunday.
At the time I’d seen hints that wearing out the internal storage was not uncommon. What I hadn’t learned, yet, was that the internal storage is a USB stick. My discovery of this was accidental — I was mucking around on my new UNVR and decided to run lsbusb -tv and there it was.

With a quick search of the Googles I found fresh knowledge that it is, in fact, a generic USB stick, and that replacing it is as simple as putting in a blank drive and holding the Reset button on boot. I guess they learned some lessons from the EdgeRouter Lite USB failure debacle. Just. Not the lesson that they should never put a USB stick in a device!


I’m tempted to hack this “extra” UNVR into a NAS, though I have concerns about what could go wrong if the USB fails again. I’ve had great luck with Samsung Fit drives but maybe an M.2 SATA SSD in a USB adapter would be a better option.
Isolating UniFi Devices
I’ve been lax in firealling my VLANs at home, but with the recent controversy over UniFi devices phoning home without consent, this has taken on renewed importance. I’m also taking on a new tenant in my detached apartment and would like to keep all their stuff segregated from mine.
Fortunately it’s all pretty easy.
For my network, I’m keeping my Cloud Key and Pi-Hole on the main LAN. I have additional Corporate VLANs created for Management, Cameras, and the Apartment.
In the Firewall rules, for WAN_OUT I’ve created two rules to Drop all traffic from the Management and Cameras networks. They cannot reach the Internet at all.
To allow and deny particular cross-VLAN traffic, the first step is to create a group of all the Private IP address ranges:
- 10.0.0.0/8
- 192.168.0.0/16
- 172.16.0.0/12
- 100.64.0.0/10 (this is CGNAT, might be a bad idea if your ISP uses them)
Back in the Rules area, LAN_IN needs a series of rules:
- Allow (Management | Cameras) networks access to the CloudKey.
- Allow (Management | Cameras | Apartment) networks access to the Pi-Hole.
- Drop (Management | Cameras | Apartment) networks access to the Private IP ranges group.
The Allow rules must be before the Deny rules for each Network.
The gotcha with denying devices access to the Internet is that they cannot directly obtain firmware updates. For UniFi Networking products this can be worked-around by having the UniFi Controller cache the firmware prior to upgrading — see Settings -> Maintenance -> Firmware.
I’m not sure whether Protect can distribute firmware updates to the Cameras. Guess I’ll find out the next time there’s an update available. Once my UniFi Protect NVR arrives I will place that in the Cameras VLAN so that traffic doesn’t have to cross the router and figure out the WAN_OUT / LAN_IN firewall rules needed to keep it happy.
UniFi Protect NVR
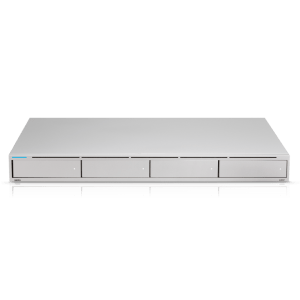 A bigger NVR for UniFi Protect finally hit the Early Access store early this morning… and was sold out by afternoon. Four LFF/SFF bays, support for RAID1 and RAID5, 1x GbE and 1x 10GbE SFP+ ports, and a port for the UniFi SmartPower Redundant Power System (also in EA). No details on the CPU or RAM but I’d presume it’s the same platform as the Cloud Key Gen2 Plus.
A bigger NVR for UniFi Protect finally hit the Early Access store early this morning… and was sold out by afternoon. Four LFF/SFF bays, support for RAID1 and RAID5, 1x GbE and 1x 10GbE SFP+ ports, and a port for the UniFi SmartPower Redundant Power System (also in EA). No details on the CPU or RAM but I’d presume it’s the same platform as the Cloud Key Gen2 Plus.
At $299 in EA it seems like a decent enough value.
I’ve ordered one, as I’m just finally starting to put Protect to real use in my backyard and the 5TB max drive size on the CKG2+ will soon be a problem. Hopefully I’ll find time to get the rest of my G3 Flex cameras up before the New Year.

UDM Pro thoughts
 I finally broke down and added the UDM Pro to my Ubiquiti router lab. Here are the specs as provided in the Early Access store:
I finally broke down and added the UDM Pro to my Ubiquiti router lab. Here are the specs as provided in the Early Access store:
- 8-Port gigabit switch with 10G SFP+ port
- Dual WAN ports for redundancy and load balancing: 10G SFP+ and 1G RJ-45
- Bluetooth connectivity for easy setup via UniFi app
- Scalable UniFi Network Controller with advanced management capabilities
- UniFi Protect video surveillance NVR with 3.5″ (or 2.5″) HDD support
- Enterprise-class IPS/IDS and DPI capabilities
- 1 x 1.3″ Touchscreen display for quick status information
- Powered by fast 1.7 GHz quad-core processor
Not mentioned is that the UDM / UDM Pro use a new OS that is not derived from EdgeOS / VyOS / Vyatta. This is why I’d held off on buying one, when the UDM was first made available to Early Access back in March it was FAR from having feature-parity with the EdgeOS-based USGs. The present state of UbiOS is much closer to production-ready (by UniFi standards).
From the perspective of the USG Pro, this is a pretty serious upgrade in performance with a very minor bump in the expected MSRP. 10Gb/s inter-VLAN routing and WAN. Supposedly can hit 5Gb/s of IPS/IDS throughput — I’m underwhelmed by Ubiquiti slapping a pretty face over open source Suricata with publicly-available lists, but I seem to be a minority.
It’s also quiet. With it sitting on my desk and the LCD showing the fans at 50%, I struggle to hear it. The USG Pro, USG-XG-8, and their EdgeRouter siblings are not quiet-space-friendly.
I feel like they’ve missed the boat in a couple of areas with regards to Protect.
One, those LAN ports should have POE. As a router, those ports are of marginal value — where a $379 router is justified, it’s going to be attached to a larger switch. But as an NVR with a larger storage capacity than the Cloudkey Gen2 Plus, having 8 PoE ports would cover many deployment scenarios and would be quite valuable (12-16 ports would be better).
Two, it should have more drive bays. 2x LFF would have been nice. More LAN ports w/ PoE and 4x SFF bays could be better.
Three, it needs a USB host port for offloading footage directly to removable storage. As things stand now, pulling footage out of Protect is a pile of suck, but presumably it will get better, and being able to push footage directly to removable storage would be a great feature.
Ubiquiti has teased a larger, 4x LFF device. It’s not clear if that will be a NAS that Protect can use, or if it will run Protect directly, and they haven’t shown the back yet so we don’t know if it has PoE switch ports to act as a more traditional NVR appliance.
UniFi Protect moves away from self-installs
Much online rage has been spilled this weekend over UniFi Protect not being made available for self-installation. If you’ve not been paying attention, UniFi Protect is a new NVR platform from Ubiquiti. Presently Ubiquiti says that UniFi Video will continue to be developed and supported… but nobody expects this to continue for very long. Protect is the new hotness, and since Ubiquiti doesn’t charge for their software, it is unimaginable that they will continue putting resources towards two separate products that do the same thing.
Today, the only way to get Protect is on the UCK-G2-PLUS — which has just launched for $199 with an 8-core ARM SoC w/ 3GB RAM and an easily upgradeable 1TB 2.5″ hard drive. Support for the UAS-XG — an attractive but otherwise bog standard 1U server with a $1,999 MSRP — is coming soon.
People are miffed for a variety of reasons. The G2+ offers very limited storage options. The UAS-XG is a fair value compared to buying an equivalent server from an Enterprise vendor, but it’s incredibly expensive relative to DIY or other thrifty options. There’s presently no middle ground.
And with the UAS-XG being a standard Intel server running Ubuntu 16.04 LTS, there’s no technical reason that Protect can’t be offered for self-installs. Using Docker — as they’ve done with UNMS, and had alluded to providing for Protect during the Beta cycle — would greatly reduce the support challenges of providing self-installable software for Linux.
I’m not sure how I feel about this. I have 5 UVC-G3-Flex cameras that I have been planning to deploy on the G2+ w/ Protect, with the expectation that if I was happy with the platform over time I would replace 6 Ring Spotlights, 4 Amazon CloudCams, and probably add a couple more.
That’s all within the advertised capabilities of the G2+, but with its limitation of a single 2.5″ drive it won’t be able to meet my continuous recording retention targets. I happen to have a 2nd G2+ already so maybe this isn’t a total deal-breaker for me, if it turns out that I really love Protect, but right now I’m questioning if Ubiquiti’s camera platforms are worth the lock-in and premium pricing.
I already have an NVR server that is substantially more powerful than the UAS-XG, an unlimited camera license for Sighthound, and a bunch of Reolink cameras from my old house which are comparable in quality to the G3 Flex.

